When it comes to improving the efficiency of computers, developers focus on enhancing the hardware and software capabilities. However, when attacked by malware, the functionalities of the hardware and software can be inhibited. This holds true for quantum computers too.
Despite the availability of various cybersecurity solutions, we continue to witness an increase in cyber-attacks and data breaches on a daily basis. While we leverage machine learning tools to fend off cyber threats, cyberattackers are also busy coming up with new and more powerful forms of malicious attacks. But this is not where the security concerns end.
At present, data is transferred as packets on the internet, from one end to the other. These data packets are generally encrypted and have public-key cryptography (PKC). After receiving the data packets, the receiver reassembles and decrypts them using PKC. While the existing encryption methods are fairly a safe solution, once quantum computers become mainstream, offering internet security using only PKC will be challenging.
Hence, scientists are working on technologies to protect against quantum computer attacks and to improve quantum security.
The following are two popular quantum cybersecurity solutions in use at the moment:
- Quantum-safe cryptography: Also referred to as post-quantum cryptography, it creates novel cryptographic techniques that can be implemented on today’s classical computers but are immune to assaults from quantum computers in the future. One method is to increase the size of digital keys such that the number of permutations that must be searched using raw computational power increases dramatically.
- Quantum key distribution: It is the act of establishing a shared key between two trusted parties utilizing quantum communication so that an untrusted eavesdropper cannot learn anything about the key. This is accomplished by sending data using photons of light rather than bits, allowing firms to take advantage of photons’ no-change and no-cloning properties. This helps firms to send a confidential key that cannot be covertly duplicated or intercepted between two parties.
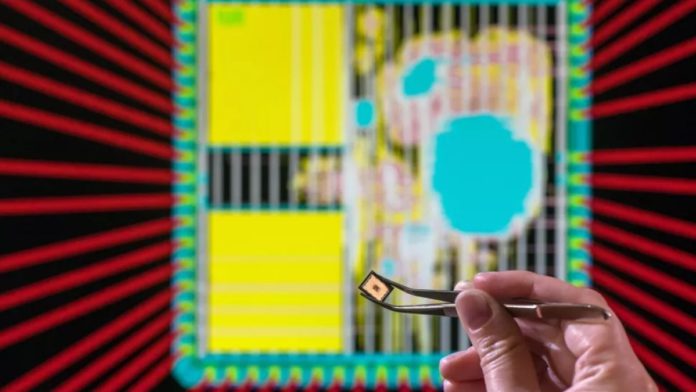
Recently, Technical University of Munich (TUM) researchers have created a computer chip that efficiently supports post-quantum cryptography and has four hardware trojans.
The chip is an application-specific integrated circuit (ASIC) that is based on the open-source RISC-V standard and is a modification of an open-source chip design. The ASIC’s design was preferred with an aim to show that it can thwart attempts by hackers to decode communications using quantum computers.
The TUM researchers claim that their chip is the first post-quantum cryptography device built fully using hardware and software co-design. As a consequence, encrypting using Kyber is around ten times faster. According to Georg Sigl, a TUM researcher who conducted the research, it also consumes around eight times less energy and is almost as flexible. The team published these results in 2020 in the journal IACR Transactions on Cryptographic Hardware and Embedded Systems.
Kyber is a lattice-based post-quantum cryptography algorithm that is also one of the promising candidates for post-quantum cryptography compared to chips based entirely on software solutions. In most cases, a lattice-based cryptography algorithm chooses a target point in a lattice on which a secret message is built. The algorithm then adds random noise to this point, making it similar to but not identical to another lattice point. For both classical and quantum computers, identifying the original target point and the accompanying secret message, without knowing what noise was added is difficult — especially when the lattice is exceedingly big.
Furthermore, processes like generating randomness and multiplying polynomials in lattice-based cryptography algorithms can use a lot of computing resources. As a result, the chip’s hardware and control software were designed to function together to generate randomness and minimize polynomial multiplication complexity efficiently.
The processor can also execute the SIKE algorithm, which needs a lot more processing power. According to the team’s design estimates, SIKE can be implemented 21 times quicker than chips utilizing solely software-based encryption. Even if someday lattice-based methods are considered no longer secure, SIKE can be viewed as a potential alternative. The team mentioned such findings in 2020 in the Proceedings of the 39th International Conference on Computer-Aided Design.
Apart from Kyber and SIKE acceleration, the research team is also using this chip as an accelerator for smart hardware Trojan detection. The idea behind incorporating hardware trojans on the chip was to explore approaches for detecting this sort of “malware from the chip factory.”
In layman’s terms, hardware trojans are additions or alterations to the circuit that are introduced to cause havoc by changing the system’s intended function. When Trojans are activated, they have a negative impact on electronics, resulting in decreased dependability, system failure, remote access to hardware, sensitive data leaking, and incurring damage to a company’s reputation.
Therefore, if attackers are successful in embedding trojan circuitry in the chip design before or during manufacture, the results might be devastating. To make the situation worse, hardware trojans are engineered to go untraceable to conventional testing practices, optical verification methodologies and evade post-quantum cryptography.
Read More: Google Announces Creating Time Crystal Inside its Sycamore Quantum Computer
While there is one proposed solution of using golden chips for microscopic inspection and comparison with suspicious hardware trojan infected chips, very little is known about how hardware trojans get included or are used by attackers. To understand more about them, the researchers included four separate hardware trojans on their device, each of which operates in a unique manner.
Sigl explains, “To develop protective measures, we have to put ourselves in the shoes of attackers, so to speak, and develop and hide Trojans ourselves. That’s why we have built four Trojans into our post-quantum chip that we developed and that work quite differently.”
In the following months, Sigl and his colleagues will evaluate the chip’s cryptography capabilities, as well as the operation and detectability of the hardware Trojans. Post that, the chip will be dismantled for research reasons. This will be accomplished by layer-by-layer destroying their proof-of-concept chip while taking individual photos of the layers then feeding each stage of the process to freshly created machine learning algorithms. This procedure will enable training algorithms to reconstruct the exact functioning of chips via reverse engineering and recognize hardware functions even in the lack of technical information about what the hardware performs.
The above findings are published in Proceedings of the 18th ACM International Conference on Computing Frontiers (2021).